Security generically refers to the possibility of ‘protecting’ information, which is either stored in a computer system or transmitted on a network.
Security properties
There are many different aspects we might want to protect. We list the most important ones below. Each of them correspond to a different security property:
- Confidentiality (or secrecy): information should only be accessed (read) by authorized entities;
- Integrity: information should only be modified by authorized entities;
- Authenticity: an entity should be correctly identified. This may apply to different settings. For example, the login process allows for authenticating a user, a digital signature (that we will discuss) allows for authenticating the entity originating a message, and so on;
- Non-repudiation: an entity should not be able to deny an event. For example, having sent/received a message. This property is crucial for e-commerce, where ‘contracts’ should not be denied by the parties;
- Availability: information should be available/usable. This property is important to guarantee reliability and safety. Apart from attacks, availability might be lost in case of faults. This is addressed through techniques that make the system fault-tolerant and that we will not treat in this course.
There are, of course, many more properties that we do not mention here and we will not have time to address in this course. Examples are fairness of contract signing, privacy, anonimity and unlinkability.
Typical attacks
We assume information is flowing from a source to a destination. For example, reading data is a flow for the data container (e.g. a file) to a user while writing (or modifying) is a flow from a user to the file system, an so on.

Malicious users might try to subvert the above properties in many different ways. We now give very general classification depending on how an attacker might interfere on the expected flow of information.
- Eavesdropping (or interception): the attacker gets access to information. This can be depicted as an additional flow towards the attacker:
- Modification: the attacker modifies information. To modify information, the attacker first intercepts it:
- Forging: the attacker introduces new information. This is usually related to impersonation since the attacker lets the destination believe the information is coming from the honest source:
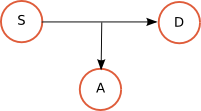
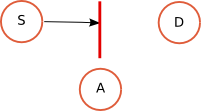
- Interruption: the attacker stops the flow of information. This is typically a denial of service that makes the system/network unusable:
Examples
We give two simple examples of attacks to show how the general scenarios above apply.
- A Trojan Horse is a program that seems to behave as expected but incorporates malicious code (such as the Greek force hidden inside the mythological Trojan Horse as described in the Virgil’s Aeneid). These programs are usually obtained by modifying existing, honest programs. This is in fact an example of modification attack in which S is the web site where the honest program H can be downloaded and D is the final user. The attacker downloads the honest program, modifies it and sets up a fake download site where D will download the Trojan Horse program.
- Suppose a bank B is using the following simple protocol to allow a bank transfer from user Alice (A):
A -> B: signA(“please pay Andy 1000 Euros”)
where signA is some “signature” mechanism to ensure that the message really comes from Alice. We thus assume that the attacker cannot generate valid signed messages from Alice. However, it is always possible for the attacker to intercept the whole message and repeat it as many times as he wants, without modifying it. This attack, called replay, consists of an interception plus forging (in this case a very simple one as the message is just re-sent as is):

The attacker Andy intercept the signed message and then replays it In this way Andy gets the bank transfer as many times as he wants by just resending message M.