So far, we have considered attackers that only know the ciphertext y and try to find either the plaintext x or the key k. In practice, it is often the case that an attacker can guess part of the plaintext. Think of encrypted messages: a message always have a standard header in a certain format and it is often easy to guess part of the information in it. Thus if a message is split into blocks which are encrypted under the same key, it is reasonable to assume that an attacker can deduce part of the plaintext. Also, if a key is reused to encrypt many plaintexts, it can occur that in the future one of the plaintext is leaked (because its security is no more relevant). This gives the attacker knowledge of a pair (x,y) plaintext, ciphertext.
For these reasons, in cryptography we often consider so-called known-plaintext attacks, i.e., we assume the attacker knows some pairs (x’,y’), (x”,y”) …. of plaintexts/ciphertexts. The challenge, given y, is to find the relative x or the k.
We illustrate this kind of attacks on a classical cipher.
The Hill cipher
This cipher is polyaplphabetic and generalizes the idea of Vigenére by introducing linear transformations of blocks of plaintext. We have ![]() , while
, while ![]() is an invertible mod 26 matrix
is an invertible mod 26 matrix ![]() . Encryption and decryption are as follows:
. Encryption and decryption are as follows:
![]()
Example
Let ![]() . We have that
. We have that
![]()
![]() .
.
Now
![]() .
.
In order to find the inverse mod 26 of 5 we need to find a number in the interval [0,25] that multiplied by 5 mod 26 gives 1. This number exists and is 21. In fact ![]() . Notice that it is not always the case that the multiplicative inverse modulo exists. We will discuss this more in detail when introducing public key cryptography and RSA. We have
. Notice that it is not always the case that the multiplicative inverse modulo exists. We will discuss this more in detail when introducing public key cryptography and RSA. We have ![]() .
.
Consider the plaintext ![]() . We have,
. We have,
![]()
![]()
![]()
![]() .
.
Cryptoanalysis
Assume, now, that the attacker has m pairs of plaintexts/ciphertexts, where m is the block length. We know that:
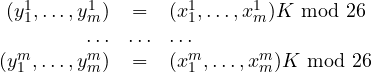
which can be written as ![]() with
with 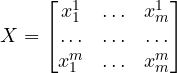 and
and 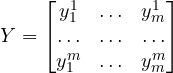 .
.
It is now clear that if ![]() exists (see the above discussion about inverse modulo) we obtain
exists (see the above discussion about inverse modulo) we obtain ![]() from which
from which ![]() .
.
Lesson learned
The Hill cipher is a linear transformation of a plaintext block into a cipher block. The above attack shows that this kind of transformation is easy to break if enough pairs of plaintexts and ciphertexts are known. Modern ciphers, in fact, always contain a non-linear component to prevent this kind of attacks.
