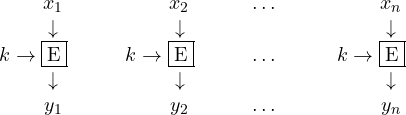
So far, we have illustrated cryptosystems that “reuse” the same key to encrypt letters or blocks of the plaintext. This is usually referred to as block ciphers.
This scheme can be generalized by considering a stream of keys instead of a fixed one. Let ![]() be such a stream. The idea is to encrypt the first letter of the plaintext with
be such a stream. The idea is to encrypt the first letter of the plaintext with ![]() , the second with
, the second with ![]() and so on. It does not matter much if we encrypt a letter or a block, the important difference is that the used key is always different.
and so on. It does not matter much if we encrypt a letter or a block, the important difference is that the used key is always different.
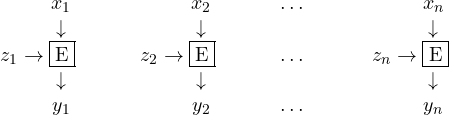
Having a different key for each letter or block of the plaintext is of course appealing but not much practical. The stream of key is thus usually derived starting from an initial key ![]() . To make the stream more complex it can also depend on previous part of the plaintext. In general we say that
. To make the stream more complex it can also depend on previous part of the plaintext. In general we say that ![]() . To understand why a key
. To understand why a key ![]() cannot depend on plaintexts with indexes greater than or equal to
cannot depend on plaintexts with indexes greater than or equal to ![]() , it is useful to reason on the decryption scheme:
, it is useful to reason on the decryption scheme:
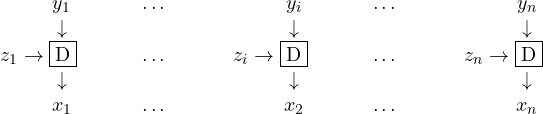
Now, ![]() meaning that we can compute it with not knowledge of the plaintext. To compute
meaning that we can compute it with not knowledge of the plaintext. To compute ![]() , instead, we need to know
, instead, we need to know ![]() . As a consequence, we have to decrypt
. As a consequence, we have to decrypt ![]() with
with ![]() before computing
before computing ![]() . Once we have this key we can decrypt
. Once we have this key we can decrypt ![]() and compute
and compute ![]() , and so on. The values are thus computed in the following sequence:
, and so on. The values are thus computed in the following sequence: ![]() . It should be evident, now, that we cannot let
. It should be evident, now, that we cannot let ![]() depend, e.g., on
depend, e.g., on ![]() as we would need that plaintext to compute the key.
as we would need that plaintext to compute the key.
Notice that block ciphers are, clearly, a simple instance of stream ciphers where ![]() for all
for all ![]() .It is also useful to classify these ciphers depending on certain properties of the key stream:
.It is also useful to classify these ciphers depending on certain properties of the key stream:
Periodic
A stream cipher is periodic its key stream has the following form ![]() , i.e., if it repeats after
, i.e., if it repeats after ![]() steps.
steps.
Exercise. Vigenére cipher can be seen as a stream cipher acting on single letters and with a periodic key stream. Formalize the cipher giving ![]() and defining the key stream
and defining the key stream ![]() .
.
Synchronous. A stream cipher is synchronous if its key stream does not depend on plaintexts, i.e., ![]() for all
for all ![]() . When this happens, we have that the key stream can be generated starting from
. When this happens, we have that the key stream can be generated starting from ![]() and independently on the plaintext. This is particularly useful to improve efficiency: we do not need to obtain
and independently on the plaintext. This is particularly useful to improve efficiency: we do not need to obtain ![]() to compute
to compute ![]() . In fact, the key stream can be generated offline, before the actual ciphertext is received.
. In fact, the key stream can be generated offline, before the actual ciphertext is received.
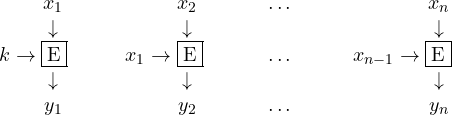
Asynchronous. This is the general case where ![]() . As mentioned above, we need to decrypt and compute the keys stream at the same time, as a key can depend on previous plaintexts. We give a simple example of a cipher of this class, called Autokey. We let
. As mentioned above, we need to decrypt and compute the keys stream at the same time, as a key can depend on previous plaintexts. We give a simple example of a cipher of this class, called Autokey. We let ![]() .
. ![]() and
and ![]() , i.e., encryption and decryption are exactly as in a shift cipher. The key stream is defined as
, i.e., encryption and decryption are exactly as in a shift cipher. The key stream is defined as ![]() and
and ![]() for
for ![]() , meaning that the first key in the stream is the initial key
, meaning that the first key in the stream is the initial key ![]() while the next keys are the same as the previous plaintext.
while the next keys are the same as the previous plaintext.
Exercise: try to break the following ciphertext encrypted with the above autokey cipher:
GUAAMLXOOVTMRVTKXOWSSDXNVJSTVTACALTNQFTPNIHUXRPWLV
